From requirements to proof – one traceable flow. Riskflow is asset-centered GRC. It connects asset context, assessments, controls, and evidence so teams can turn regulatory, legal, contractual, and internal requirements into clear control scope and audit-ready proof.
Traditional GRC often starts with catalogs, questionnaires, and isolated control work. Riskflow starts with the asset landscape the requirements actually affect.
By keeping requirements, asset context, controls, ownership, and evidence connected, teams can see what applies, what is missing, and what is proven – even as systems, services, and dependencies change.
Requirements change. Asset landscapes change. Internal controls evolve. But in many organizations, these things do not stay connected.
That is when GRC turns into spreadsheets, folders, tickets, and one-off answers. Teams lose track of what applies, what is covered, who owns it, and what can actually be proven.
Requirements drift away from operations
Regulatory, legal, contractual, and internal obligations often live far away from the assets, services, and processes they affect.
Control scope becomes unclear
Teams struggle to see which controls apply where, why they apply, and what still needs action.
Evidence shows up too late
Proof gets collected at the end instead of staying attached to the work throughout the process.
The same work gets repeated
Assessments, customer requests, and audits often trigger duplicate effort because context is not reused.
and much
more …
Riskflow was designed for regulated and audit-heavy environments where requirements need to become operational, traceable, and provable.
Built in Europe
Designed for strong regulatory environments and high expectations around privacy, security, and auditability.
Integrate, don’t replace
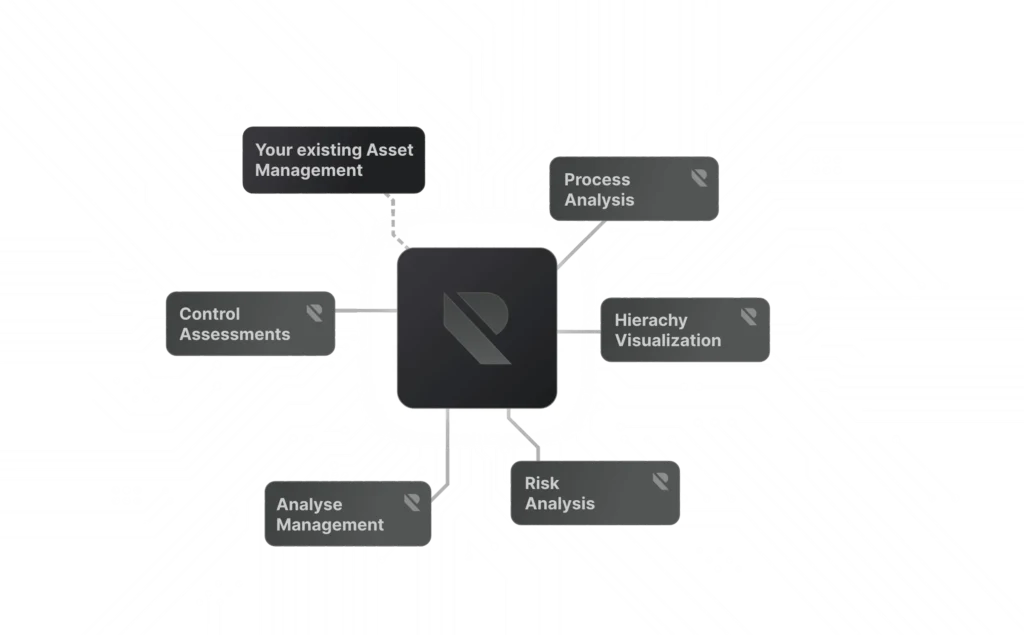
Riskflow works with the systems you already use instead of forcing another disconnected asset silo.
From requirements to controls – end to end
Riskflow connects requirements, asset context, control scope, responses, and evidence in one model.
Traceable by design
See where context comes from, how it flows, and why a control applies.
Automation that stays understandable
Reduce manual work through structure and inheritance without losing transparency.
Keep your assets in the systems you already use. Riskflow syncs the context it needs.
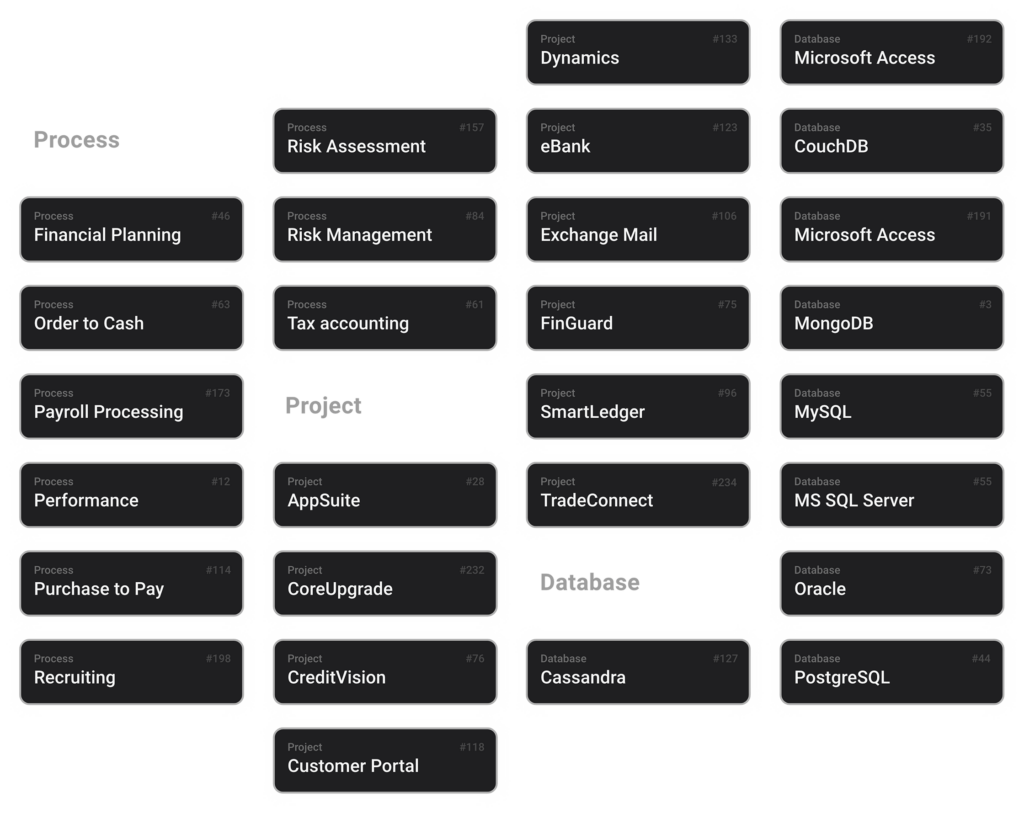
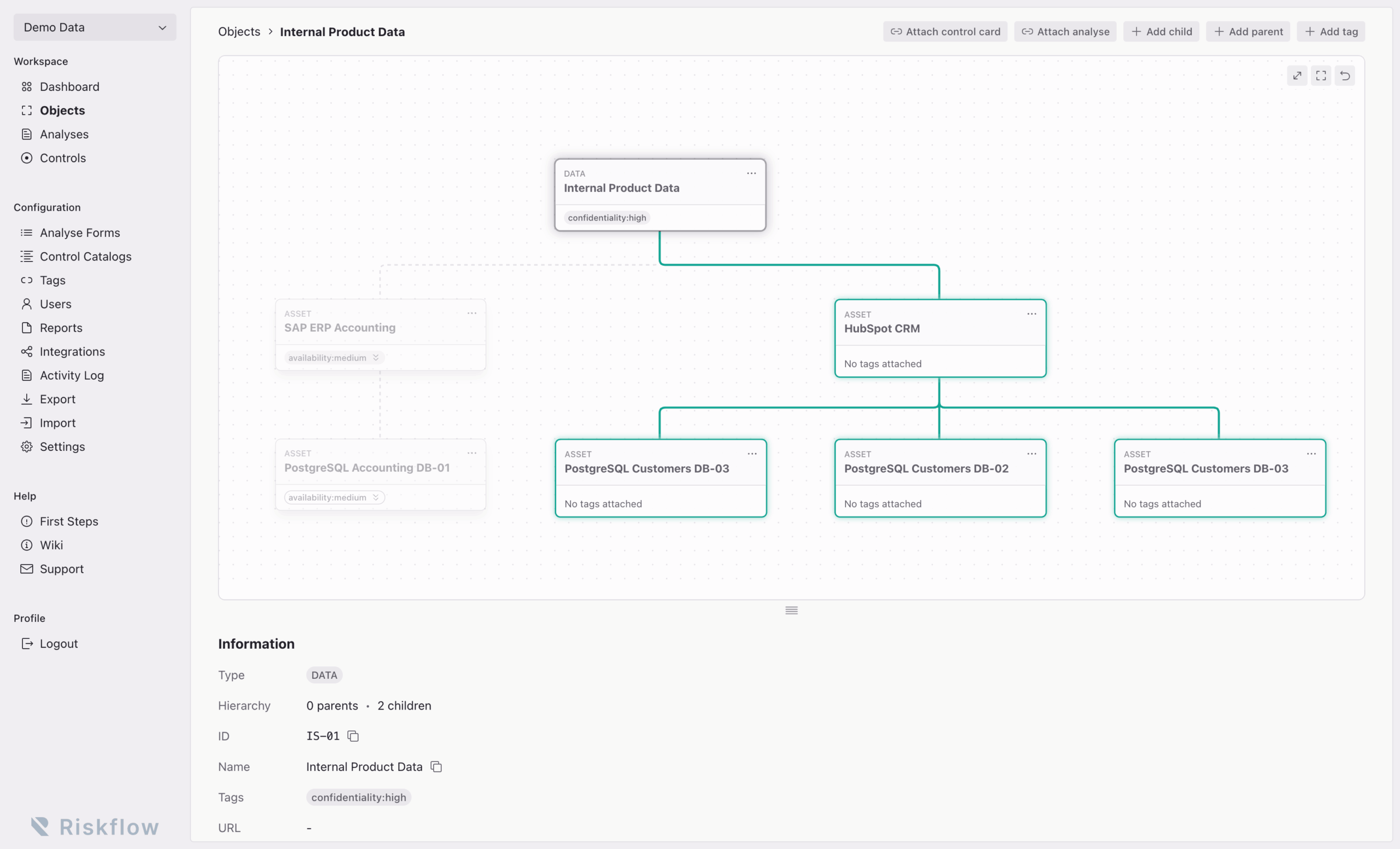
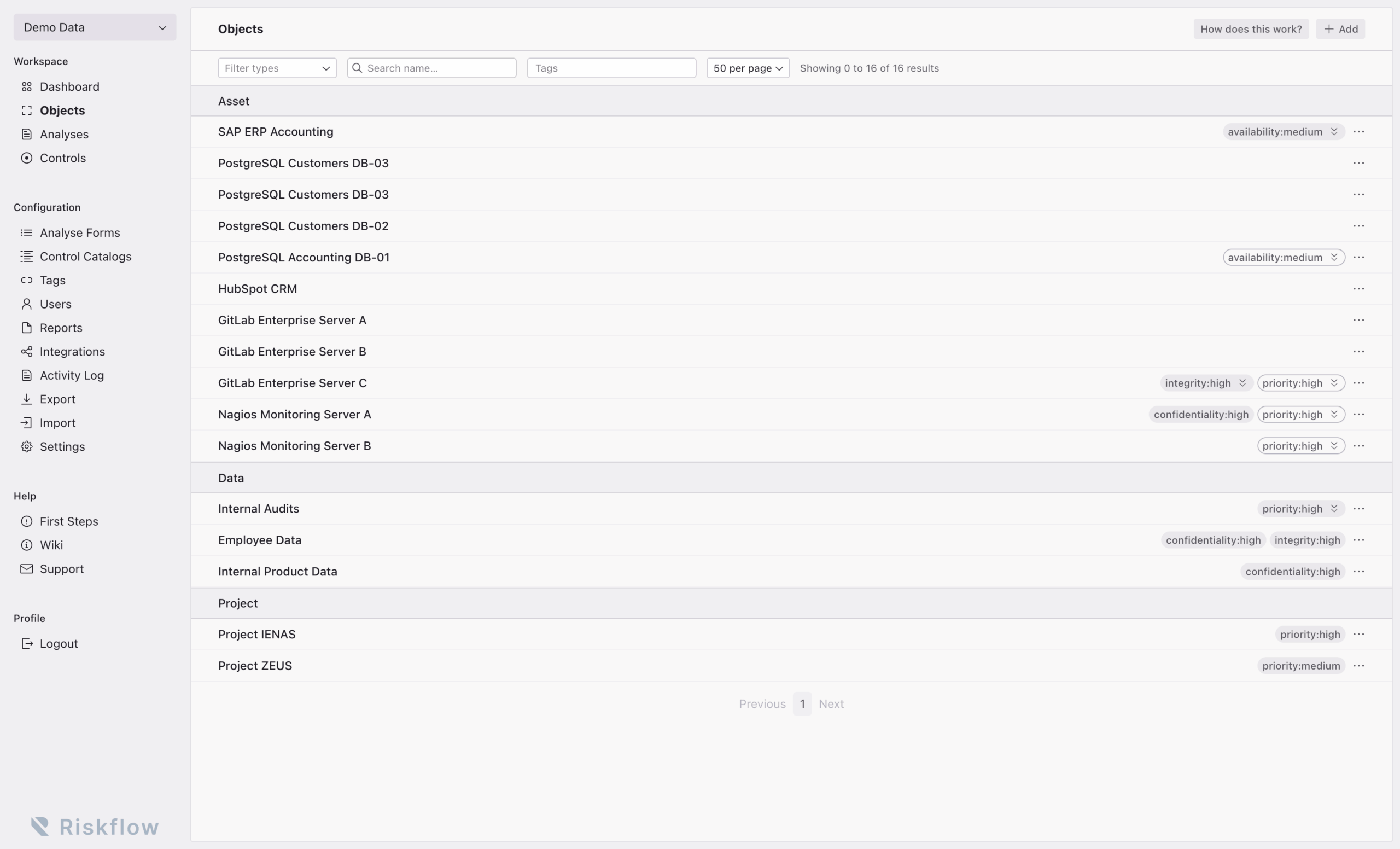
Structure assets, apply tags, and model dependencies so relevant context stays connected.
Run assessments, map controls, and see which requirements apply where.
Apply controls based on structure and relevance, not on broad assumptions or manual distribution.
Get a usable overview of control coverage, open gaps, impacted areas, and next actions.
Riskflow helps teams operationalize regulatory, legal, contractual, and internal requirements by connecting asset context, controls, ownership, and evidence in one system.
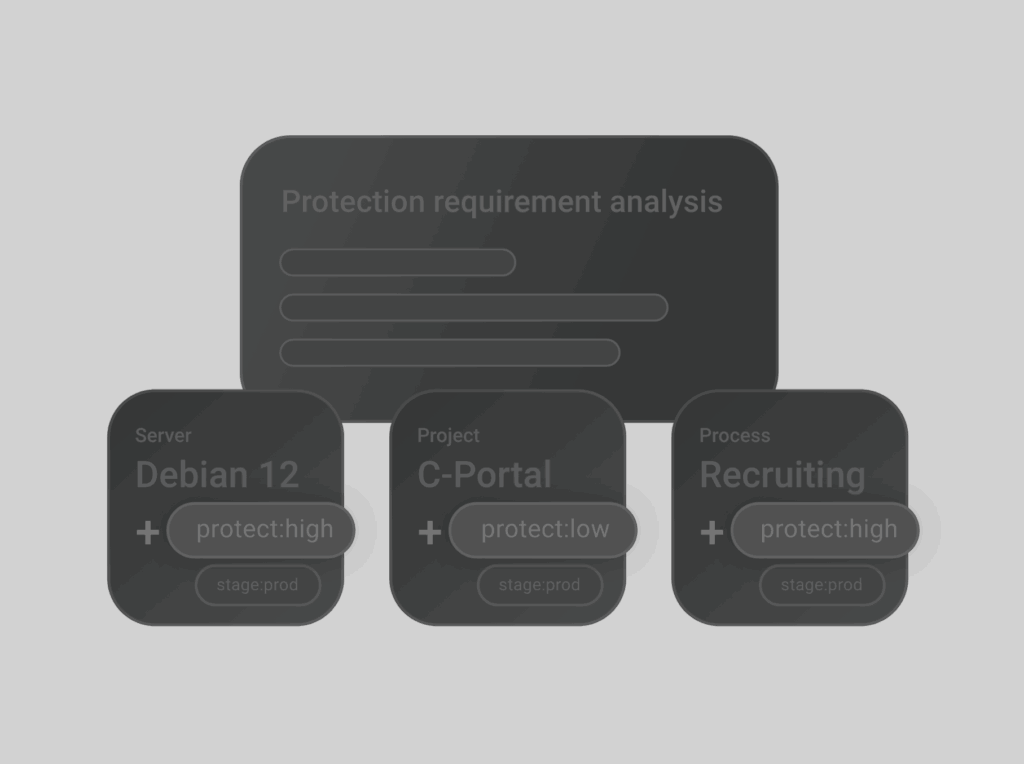
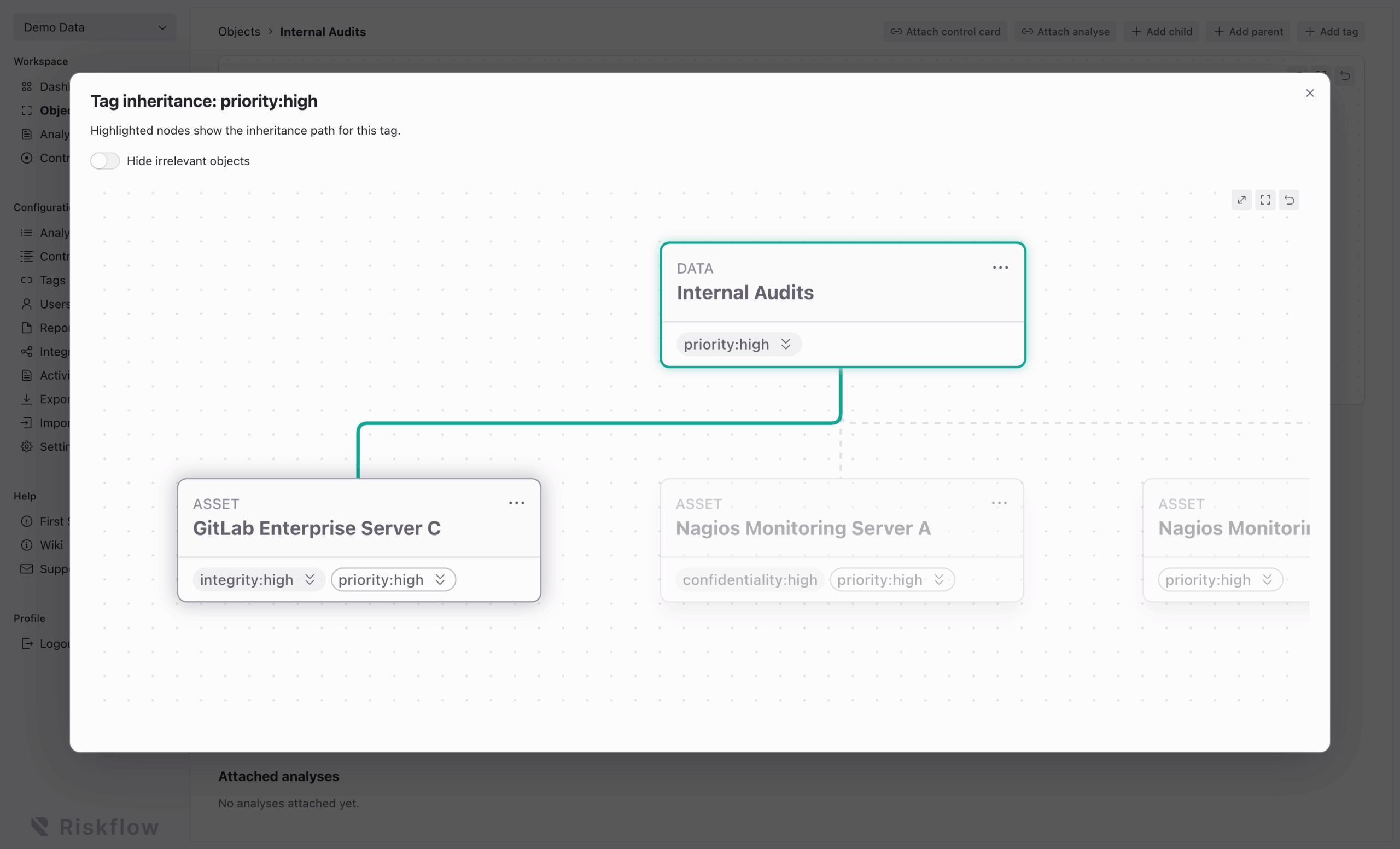
Tags carry requirement-relevant context across connected assets. This keeps control scope consistent and reduces the need to recreate the same logic object by object.
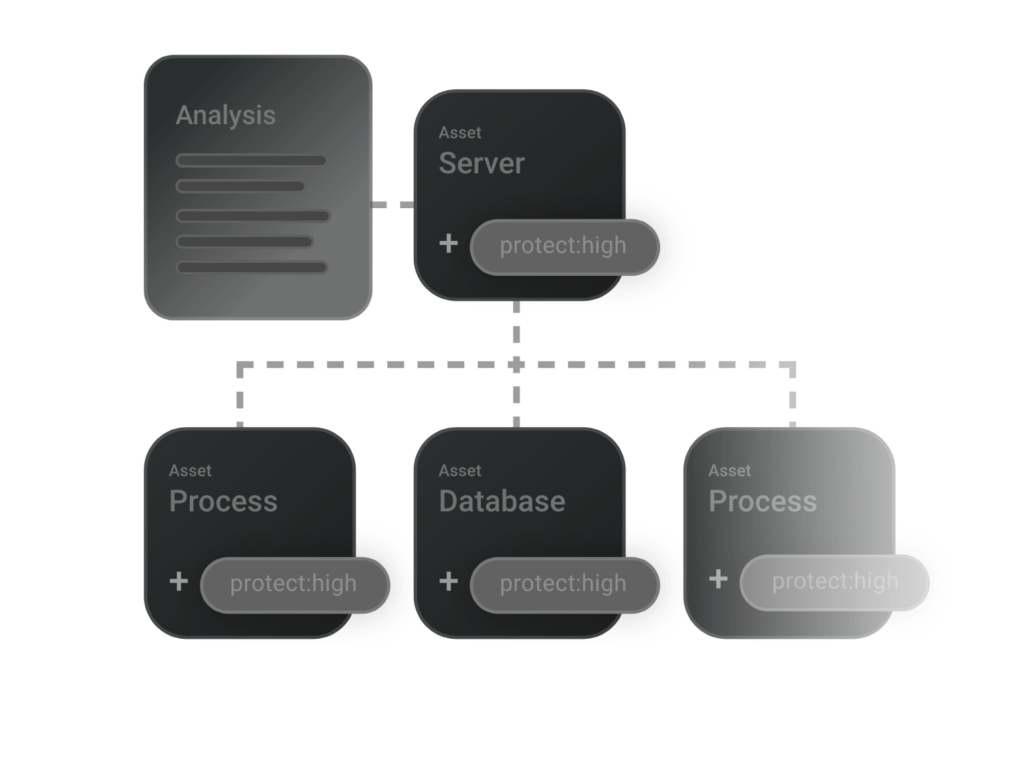
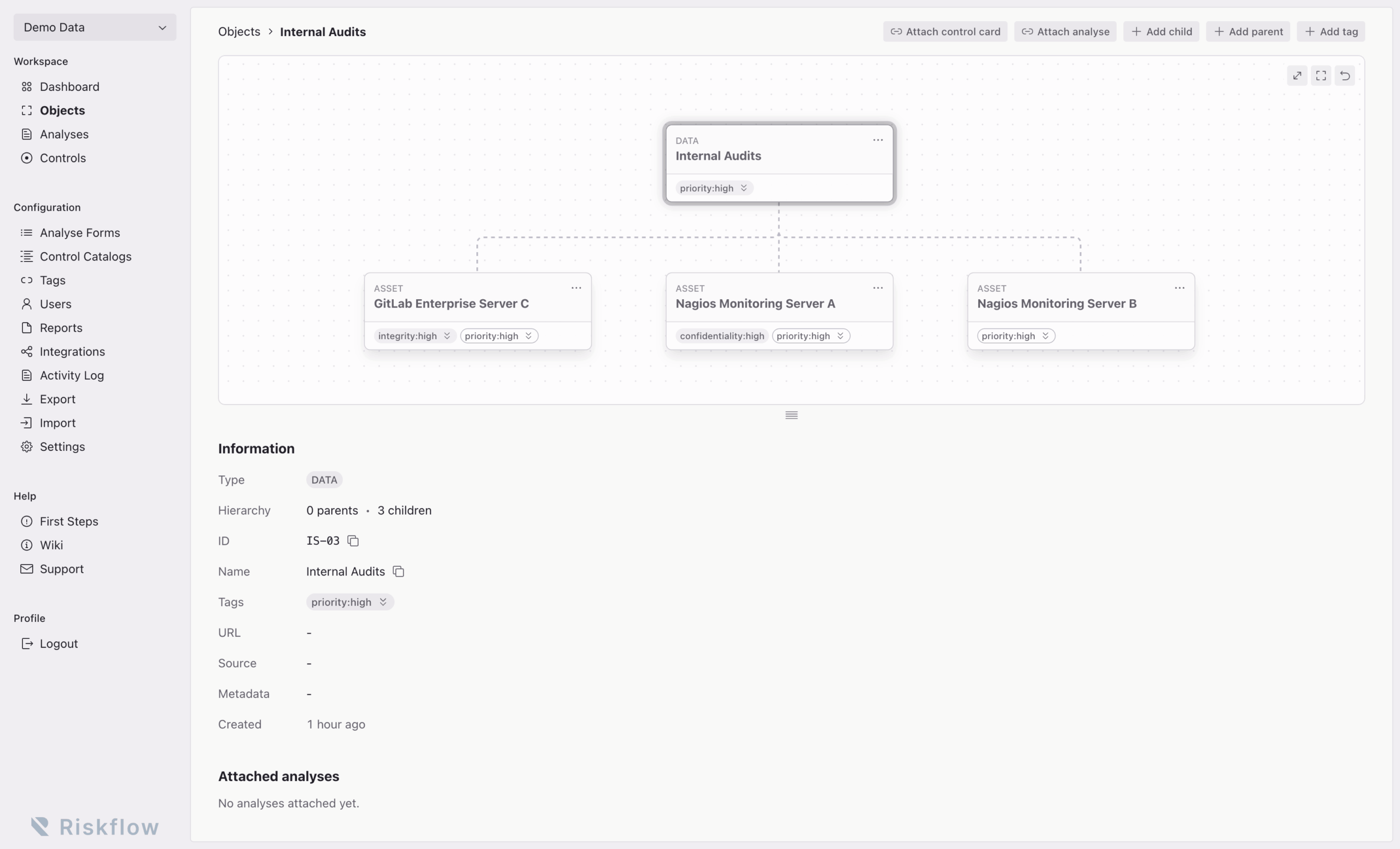
Understand hierarchies, dependencies, and ownership in one view. That makes it easier to see where requirements land and how changes affect the wider environment.
Create assessments, use templates, and attach them where they belong. Results stay connected to the asset context and can directly support downstream control work.

Riskflow is not another redundant asset database. It uses the systems you already rely on, adds traceable control logic on top, and helps you avoid managing the same data twice.
Use predefined assessments and control catalogs for common frameworks, then adapt them to your environment. That shortens setup time without forcing a rigid model.
Automatically reopen controls and assessments on schedule, keep review cycles moving, and make recurring compliance work easier to manage over time.
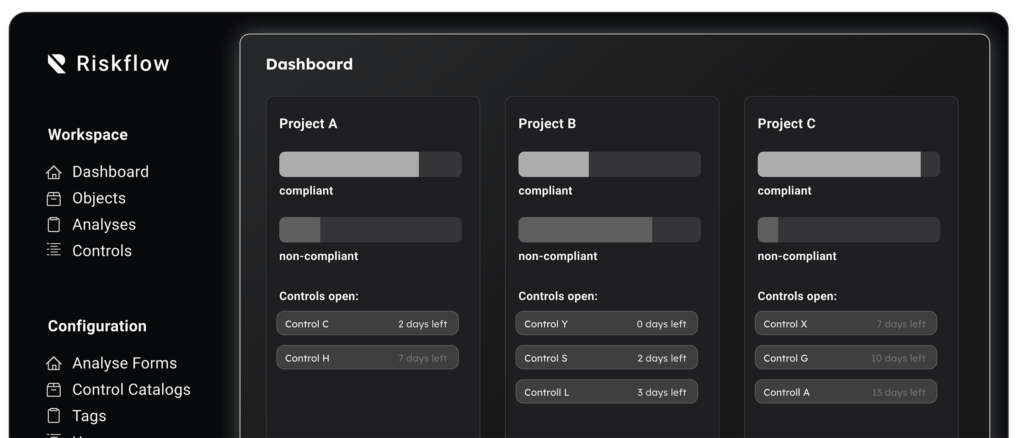
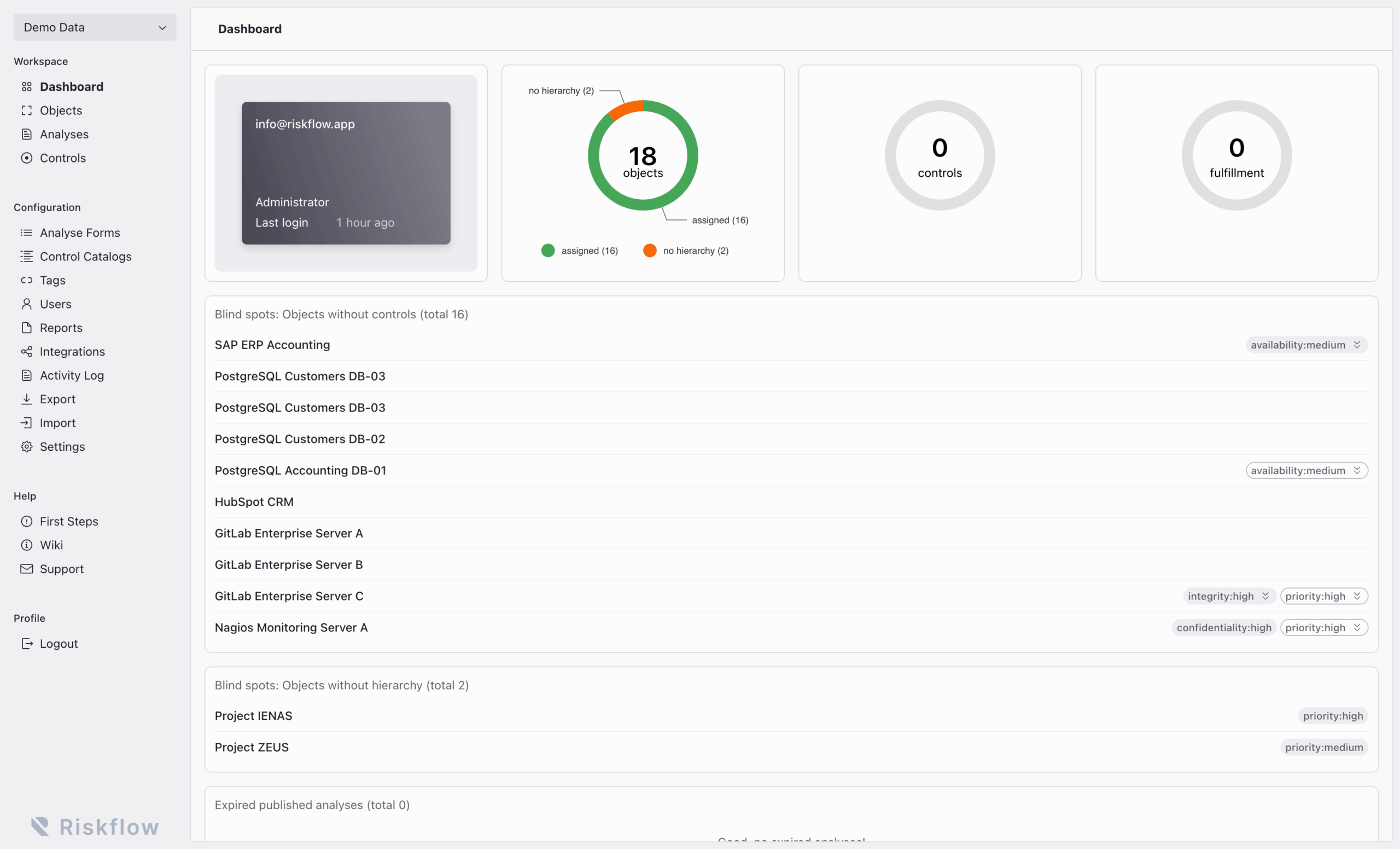
Track gaps, ownership, pending work, and current control status in one place. Teams and management get a more current view of what needs attention.
We continue to expand Riskflow based on customer needs and regulatory change.
Riskflow fits into your existing environment. Keep your operational systems where they are, bring in the context GRC needs, and turn requirements into controls, evidence, and proof in one traceable flow.
Integration principle: Integrate, don’t replace
Riskflow is built to work with your existing systems, not to compete with them. Your source systems stay operational. Riskflow adds traceable control logic, workflow, and proof on top.
Riskflow connects requirements, asset context, controls, and evidence in one traceable flow. Instead of treating GRC as disconnected questionnaires and documentation, it helps teams see what applies, what is missing, and what is proven.
Governance, Risk, and Compliance (GRC) is the work of turning regulatory, legal, contractual, and internal requirements into clear ownership, effective controls, and verifiable evidence.
Riskflow is especially suited to banks, regulated fintechs, insurers, and critical service providers. It also fits other audit-heavy teams with strong governance, control, and evidence requirements.
Riskflow helps teams operationalize regulatory, legal, contractual, and internal requirements by translating them into clear control scope, ownership, assessments, and proof.
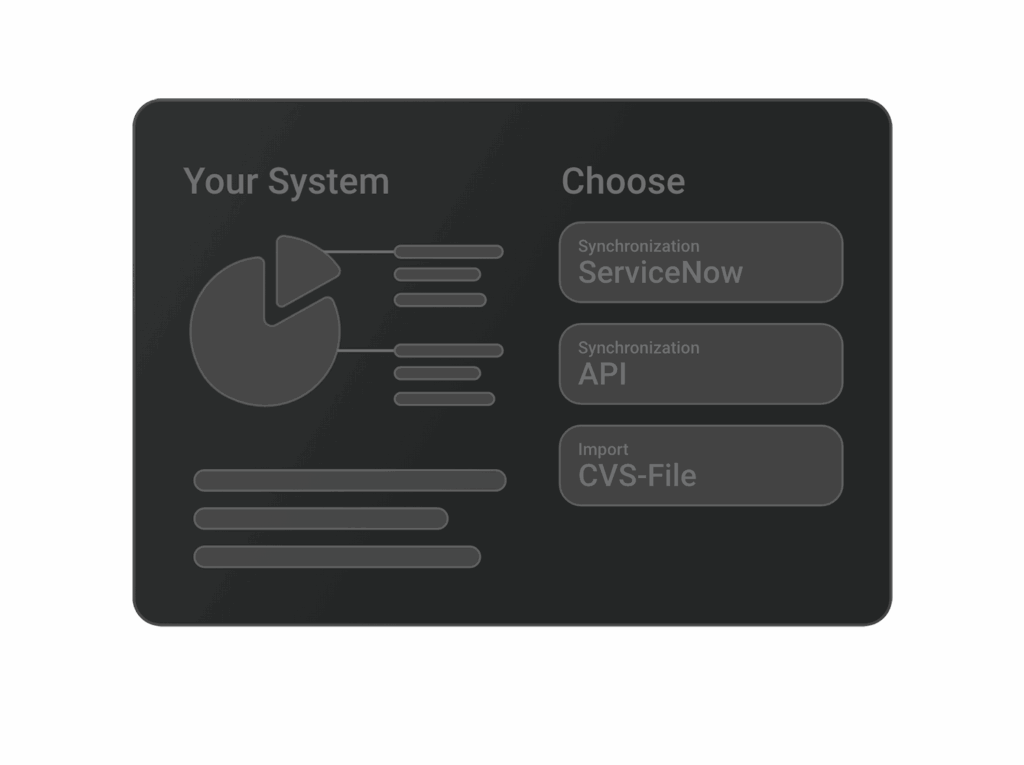
No. Keep your existing source systems. Riskflow is designed to use asset context from systems such as ServiceNow, CSV-based imports, and APIs instead of forcing another redundant asset database.
Yes. Riskflow is built to fit into existing environments through ServiceNow integration, CSV import, and APIs. The goal is to work with your stack, not replace it.
That depends on your environment and scope, but teams can often start with a focused workflow, existing data, and reusable templates rather than a large replacement project.
By connecting requirements, context, controls, and evidence in one flow. Teams can reuse structure, inherited context, and shared control responses instead of rebuilding the same logic across audits and review cycles.
Riskflow keeps the path from requirement to control to evidence traceable. That makes it easier to show what applies, what was assessed, what was evidenced, and what still needs action.
Yes. Riskflow supports cloud, on-prem, and own-cloud deployment models for teams that need flexibility in how they operate the platform.
Riskflow is built for environments that care deeply about privacy, auditability, and operational control. Security, access control, and deployment flexibility are treated as core requirements, not add-ons.
Riskflow is built to stay usable as complexity grows. Teams can work across large asset landscapes and control environments without losing structure or traceability.
Know what applies. See what’s missing. Prove what’s done.
Riskflow gives regulated and audit-heavy teams a clear view across assets, controls, and evidence – without another disconnected GRC silo.
We’d love to show you how Riskflow can streamline your security management. Contact us now via email or contact formular – we’re happy to help!
1. CSV Import: Upload a CSV file (e.g., assets.csv) to automatically populate fields such as ID, Name, and Location.
2. API Integration: Use our REST API (e.g., POST /api/assets) for real-time synchronization, ensuring your asset data is always up to date.)
3. Manual Entry: Quickly create individual assets through the user interface by entering details like Name, Category, and Description.
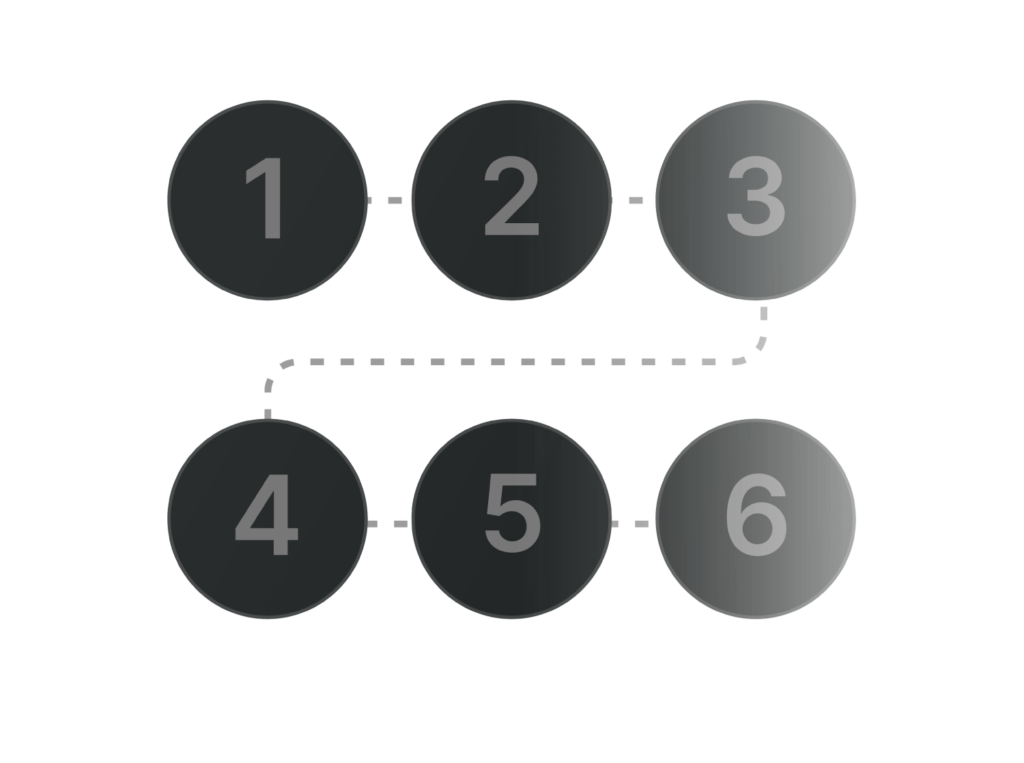
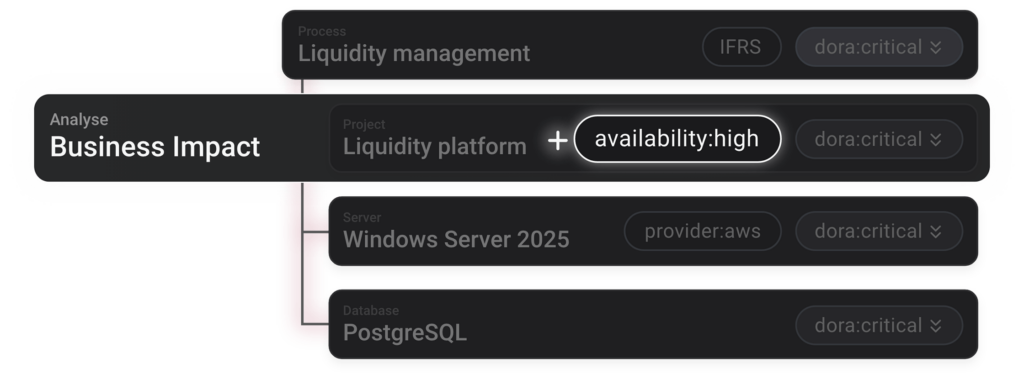
1. Link Assets: Link your assets logically (e.g., Process – Application – Server – Database – Location) to create a clear structure and reflect dependencies. You can also import these relationships directly from existing systems (CSV or API), eliminating the need to rebuild them manually.
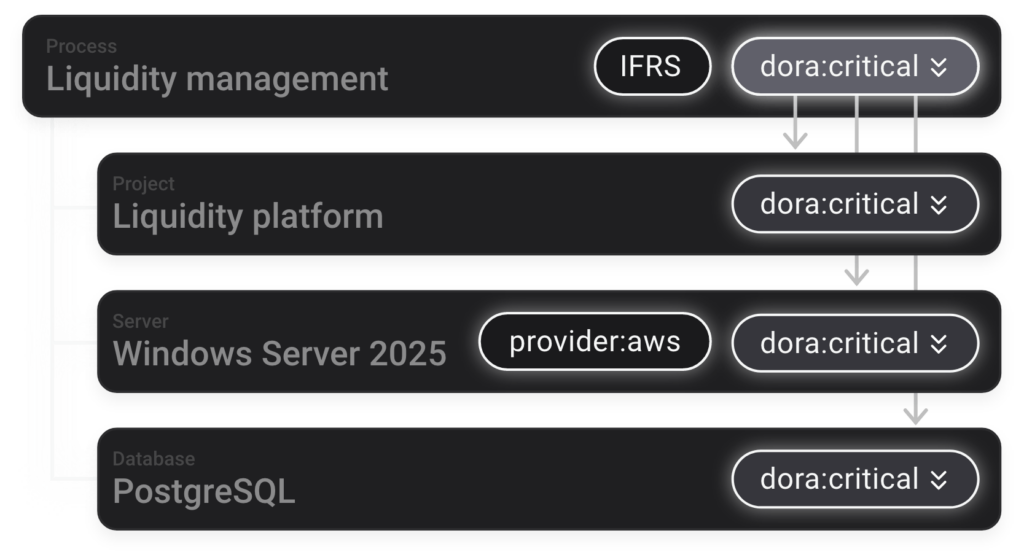
2. Assign Tags: Assign meaningful tags (e.g., DORA critical, GDPR) so that controls, reports, and other GRC processes can be applied more accurately and efficiently.
This way, subsequent processes – such as targeted analysis, reporting, or control management – can be carried out more accurately and efficiently.
1. Questionnaire Setup: Create a custom BIA questionnaire or import an existing one (e.g., via CSV).
2. Perform the Analysis: Attach the questionnaire to relevant processes or assets and gather responses to determine criticality and impact.
3. Review Results: The BIA outcomes are displayed on each asset, with any critical status or tag cascading through the asset hierarchy as needed.
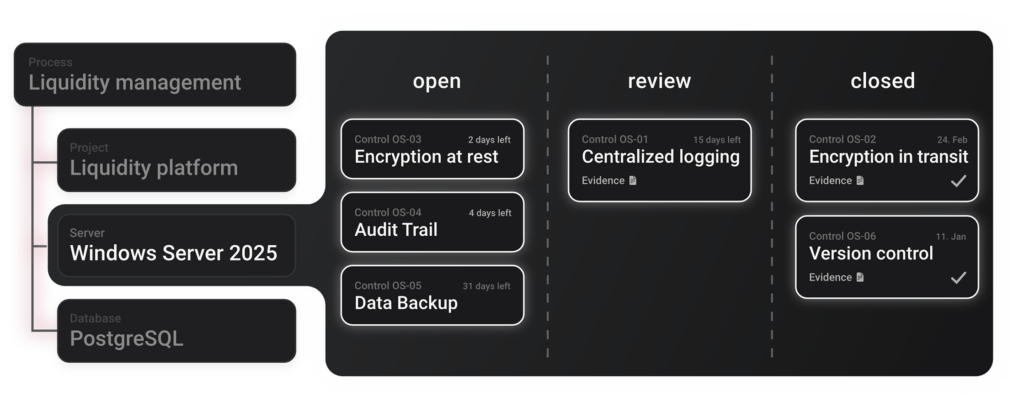
1. Identify Relevant Controls: If the BIA flags a process as critical, the system suggests matching controls (e.g., Business Continuity Plan).
2. Map Controls to Assets: Assign these controls to the tagged assets. The Critical tag ensures they inherit the right controls.
3. Monitor Gaps: Quickly see if any required controls are missing or incomplete, and act immediately to strengthen compliance.
Imagine your Process is labeled dora:critical. All linked applications and databases automatically inherit this tag, ensuring you can quickly spot high-priority assets across your environment. In the screenshot, you can see how dora:critical, along with tags like dsgvo and stage:prod, flows down from the Process level to connected systems.
If there’s a particular asset you want to exclude – because it’s not truly critical in practice – you can simply disable inheritance for that asset. This way, you maintain an accurate overview of your real risk landscape without having to manually adjust every single item. Any disabled inheritance is properly logged, ensuring traceability and providing a clear audit trail for future reference.
Our Form Editor lets you define any type of analysis – whether it’s a Business Impact Analysis, a Risk Assessment, or a Compliance Checklist. Each form can output specific tags based on the responses entered. Once submitted, your assets automatically inherit the tags that correspond to their answers or calculated risk levels.
For instance, if a form identifies a process as “critical” that tag is immediately applied to the process and, if desired, cascades down to related systems or applications. This saves you from manual tagging and helps maintain a real-time, accurate view of your organization’s risk posture.
Want to get started quickly? Use one of our ready-made templates – like GDPR or ISO-specific questionnaires – or easily build your own. Our intuitive drag-and-drop editor ensures that anyone can create robust, automated analyses without writing a single line of code.
Manage all evidence for your controls in one central location. Upload documents and document assessments to maintain an overview of your compliance status at all times. This way, everything is in one place, without having to search extensively.
Work seamlessly with other teams – whether evaluating controls, storing evidence, or commenting on results. The primary focus here is the workflow, where the responder and the overseeing unit collaborate closely. All changes are synchronized in real time, ensuring everyone remains on the same page. No more endless Excel spreadsheets, just true collaboration in a centralized system.
Our ready-to-use templates let you apply best practices instantly.
How it works:
You can expand or combine any template to suit your needs, saving time while leveraging proven best practices.
Recertification is vital for maintaining your organization’s security posture. Our system keeps track of upcoming due dates for controls and analyses, so you can review and update your measures as needed before they expire.
Our dashboard gives you a real-time overview of the compliance status and outstanding tasks in your projects, clearly showing how many controls and analyses have already been fulfilled (“Compliant”) and where further action is needed (“Non-compliant”).
GRC Software
Company
Support
Legal Information
By using control cards, all relevant requirements – even those from different catalogs – are consolidated. Instead of having to answer the same question multiple times, a single response suffices and is automatically applied to all associated objects. This saves time, speeds up the compliance process, and ensures a consistent assessment across the entire security landscape.
Different user roles (e.g., Administrator, Collaborator) can be assigned distinct permissions and responsibilities. This separation of duties supports better governance and reduces the risk of unauthorized changes or unwanted data access.
The software can be operated in the provider’s cloud, on local on-premises servers, or in a private (self-hosted) cloud environment. This flexibility allows you to choose the deployment model that best meets your security, compliance, and infrastructure requirements.
The audit log makes it possible to track at any time who made what changes and when, ensuring transparency and traceability.
Catalogs and analyses follow a structured lifecycle from draft to archive. In Draft mode, changes can be coordinated and quality improved, with the goal of publishing sufficiently quality-assured analyses and catalogs (Publish). Catalogs and analyses no longer needed are archived (Archive) but remain available for audits or references.